Cyber Attacks May Spark New War in Korea
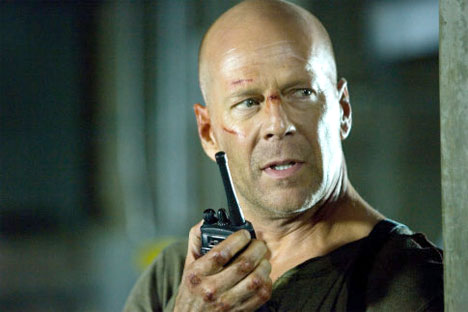 Those who are familiar with Len Wiseman’s 2007 film “Live Free or Die Hard” (“Die Hard 4.0”) will recall the actor Bruce Willis taking on a gang of cyber terrorists intent on hacking FBI computers. At one point, the arch-villain Gabriel orders a crew of hackers to start a “fire sale” by taking control of the stock market and transportation grids. The attack is designed to target the nation’s reliance on computer controls, sending the public into a panic and presenting us with an almost credible sci-fi plot. The reality of today’s world shows that cyber-terrorism, if left unchecked, might be used not only by individuals or extremist groups, but by hostile governments on the offensive.
Those who are familiar with Len Wiseman’s 2007 film “Live Free or Die Hard” (“Die Hard 4.0”) will recall the actor Bruce Willis taking on a gang of cyber terrorists intent on hacking FBI computers. At one point, the arch-villain Gabriel orders a crew of hackers to start a “fire sale” by taking control of the stock market and transportation grids. The attack is designed to target the nation’s reliance on computer controls, sending the public into a panic and presenting us with an almost credible sci-fi plot. The reality of today’s world shows that cyber-terrorism, if left unchecked, might be used not only by individuals or extremist groups, but by hostile governments on the offensive.
The Korean peninsula is now quickly turning into a place where a singular cyber-attack might spark a full-fledged conflict. Last month, North Korea was accused of actively jamming global positioning system (GPS) signals, targeting South Korea’s two largest airports outside its capital city of Seoul. The jamming signals, which were first detected on April 28 and ended on May 6, were traced to the North Korean border city of Kaesong, just 10 km north of the DMZ. Suspicions fell on imported truck-based jamming systems from Russia, capable of jamming signals within 100 kilometres. Was it really North Korea who stood behind the GPS jamming incidents and, if so, what was the purpose?
Following the North’s failed satellite launch on April 13, cyber warfare could be considered by Pyongyang as a more cost-effective way of intimidating the South. North Korea can send out jamming signals over a wide bandwidth, affecting a large number of facilities without consuming excessive amounts of energy or much needed foreign currency. A total of 553 aircraft flying in and out of South Korea’s Incheon and Gimpo airports reported GPS system failures, as did hundreds of ships and fishing boats. Considering the proximity of Seoul to the DMZ and Incheon International Airport’s proximity to the disputed waters of West Sea (Yellow Sea), such activity could cause aircrafts or ships to stray into North Korean territory, which would justify another naval clash.
GPS jamming can be used alone or in combination with other electronic and network-based attacks to disrupt South Korea’s highly digitized society. In addition to its forays into electronic warfare, the North’s military is also reportedly building up its hacking expertise. Within the last 12 months, North Korean military intelligence was accused of conducting a number of cyber attacks against South Korean and US financial institutions, government, and military websites. Experts believe that the DPRK People’s Army has units with hundreds of hackers, many of them based in China, who are employed in psychological operations to spread propaganda and infiltrate social networks. The Reconnaissance General Bureau is usually suspected of being responsible for coordinating these attempts to take down South Korea’s IT and communications infrastructure.
While inter-Korean confrontation is reaching new heights, the arrest of a 56-year-old naturalized citizen of New Zealand in Seoul in June reveals a new trend in an old conflict. An ethnic Korean known as “Mr. Kim” has been accused of exporting a satellite navigation system and long-range rocket detectors, which could have seriously compromised South Korea’s military capability. Kim and his South Korean business partners were arrested after an alleged meeting with a North Korean agent in Dandong, China. In July of last year, Kim also engaged in trade activities in Nampo, North Korea, where he handed over sensitive information that had been requested by a North Korean agent.
To what extent the North Korean military was able to utilize this equipment and information became clearer in early June this year. In an unusually detailed statement, the General Staff of the Korean People’s Army declared an ultimatum to the South Korean president Lee Myung Bak. It claimed that its missile units and other forces had been programmed with the longitude and latitude co-ordinates of various media outlets in Seoul. Among the named targets were the Chosun Ilbo and JoongAng Ilbo newspapers, a TV channel operated by the Dong-A Ilbo newspaper, and the KBS, CBS, MBC, and SBS television stations. In its report, the Korean Central News Agency (KCNA) named specific coordinates of the targets and promised to eliminate them if Lee did not publicly apologize for “hurting the dignity of the supreme leadership of the DPRK.”
According to Martyn Williams, who runs the “North Korea Tech” website, the coordinates given by the KCNA for the Chosun Ilbo and Dong-A Ilbo were incorrect, in that they failed to factor in the simple rule that the maximum value for measuring minutes and seconds is 60. That is, the Chosun Ilbo was listed at 37°56’83″ North and 126°97’65″ East. Even if these calculations were corrected and processed through mapping software, one would end up in the mountains to the northwest of Chuncheon province—a long way from downtown Seoul. The Dong-A-Ilbo’s location was similarly mistaken, as well as the coordinates of JoongAng Ilbo office, which in fact, belonged to a building across the street.
However, it is not only the hi-tech GPS equipment that North Korea might use to cause chaos and panic in South Korea. Some computer experts say that the North could try to destroy infrastructure in South Korea connected with traffic, electricity, power plants, and water supplies by hacking into computer systems. Over the years, the arsenal of North Korean cyber warfare has expanded to include virus-laden computer games. A 39-year-old South Korean game distributor, known as “Mr. Cho,” is now in police custody for allegedly violating the National Security Law when he travelled to Shenyang, China, where he is said to have met with agents of a North Korean trading company.
Cho asked the North Korean programmers to develop game software that would be used in South Korea, purchasing dozens of copies valued at tens of millions of Korean won. He then sold them to South Korean distributers. According to South Korean intelligence officials, these games were infected with malignant viruses, which turned customers’ PCs into “zombie computers,” contributing to the attempted cyber attacks against Incheon International Airport in March 2011. This activity could also provide the North with the personal information of hundreds of thousands of South Korean users of online games.
Unlike the GPS-guided conventional strike, a cyber-attack can be much more precise, long-ranged, and frustrating. North Korea-focused websites run by Pyongyang watchers and academics often fall victim to hacking attempts, which usually take the form of a Distributed Denial of Service attack. DDoS attacks involve surging a server with unwanted requests, creating such demand on the processor that the website itself becomes unavailable. Tad Farrell’s web portal “NK News: DPRK Information Center” suffered several such attacks in the past before being knocked out completely on June 6 by a different type of malicious attack where passwords were changed and most of the data in the server was wiped out.
It happened just two days after a rare photo of Kim Il Sung was published online, revealing the huge cyst on the neck of the former North Korean leader. Talking about this tumor is considered a crime in the North, and the DPRK media still meticulously avoids depicting it. Was this attack initiated by the North Koreans? It is always very difficult to find the culprit of any cyber attack. The North is routinely blamed for masterminding cyber attacks against the unfriendly sites, particularly if they are linked to North Korean defectors or focused on human rights issues. The paranoid nature of the South’s spy agencies and the ongoing inter-Korean conflict tend to elevate such suspicions to the status of common knowledge.
Cyber-attacks occur regularly worldwide and Trojan viruses are relatively easy to code. To organize and sustain a DDoS attack, the hackers must have resources on the scale that could only be provided by a wealthy client or a nation state. With heightening tensions in mind, North Korea would certainly do everything in its power to bolster its intelligence gathering capability along with the ability to attack vulnerable targets. But would not South Korea or China do the same? Even rogue NGOs with sufficient funds and vested interests can be linked to cyber crime.
For example, another news portal that follows North Korea, The Daily NK, reports that it knows the source of the malware infections installed on its website because the same Trojan scripts can be found on Chinese registered domains digtaobao.com and 10086chongzhi.com. These sites have no content and could be used by squads of international hackers. But just because a script is associated with China, does not necessarily answer the question about the origin of the malware code. The reasons behind each attack are much more obvious then the identity of a culprit. In most cases, cyber attacks leave us with circumstantial evidence but never with a smoking gun.
Still, following the most recent incidents, South Korean prosecutors will look even closer at any possible relations between the arrested suspects and North Korea’s jamming of GPS signals and cyber attacks. In a divided Korea, espionage can mean the death penalty. Although no one has been executed in the South for any crime since 1997, the new age of burgeoning information and communication technologies presents new challenges to states and national security. More peoples’ lives become vulnerable to subtle technological manipulations, and even foreign nationals can be easily accused of conspiring with the enemy or targeted by the conflicting sides.
The damage from cyber warfare can be serious and its potential consequences are yet to be understood worldwide. A Russian specialist on information security, Eugene Kaspersky, warns: “A cyber weapon can replicate itself and hit a random victim anywhere around the world, no matter how far you are from the conflict zone. After all, the Internet has no borders and an attack may target an identical system, for example power stations, even if they are located in a very different region of the world.” In other words, cyber terrorism opens a new Pandora’s Box of dangers of which the world has not had a chance to witness except from hypothetical scenarios in the Hollywood blockbuster “Die Hard 4.0.”
Peace and security in Korea is becoming increasingly susceptible to cataclysms, which can be triggered by either a malicious intent or human mistake. The non-aggression and non-nuclear agreements, which were signed by Seoul and Pyongyang in the early 1990s, as well as the suspension of mutually hostile propaganda, which was maintained during the years of “Sunshine Policy” (1998-2008), are now null and void. Any provocation—either real or assumed—can be fatal and can lead to the resumption of a full-scale war on the densely populated peninsula.
The Armistice Agreement signed in Korea in 1953 is long over-due for replacement by a firm peace treaty, which would guarantee security and create conditions for peaceful co-existence of the two Korean states. Reconciliation and collaboration between Koreans and their neighbors is necessary to avert the danger of a man-made regional catastrophe. Failing to achieve it quickly, means the whole world might be caught in the virtual crossfire of an unfinished civil war, which began 62 years ago.
