Intangible Transfer of Technology (ITT): Open-source Information Analysis for the Implementation of Sanctions on North Korea
 According to the latest reports by the United Nations (UN) Panel of Experts (POE) on North Korea, academic collaboration with North Korean individuals or entities could entail potential proliferation risks through the intangible transfer of technology (ITT). ITT involves transferring or making controlled items available to an entity or individual via intangible means, such as email, verbal communication, training or visual inspection. For instance, data related to sensitive experiments can be shared with North Korean entities via email or cloud computing services, or North Korean individuals could gain experience in dealing with controlled equipment through training provided by foreign experts. Controlling ITT may play a significant role in slowing down North Korea’s progress in developing weapons of mass destruction (WMD).
According to the latest reports by the United Nations (UN) Panel of Experts (POE) on North Korea, academic collaboration with North Korean individuals or entities could entail potential proliferation risks through the intangible transfer of technology (ITT). ITT involves transferring or making controlled items available to an entity or individual via intangible means, such as email, verbal communication, training or visual inspection. For instance, data related to sensitive experiments can be shared with North Korean entities via email or cloud computing services, or North Korean individuals could gain experience in dealing with controlled equipment through training provided by foreign experts. Controlling ITT may play a significant role in slowing down North Korea’s progress in developing weapons of mass destruction (WMD).
To mitigate the potential proliferation threat posed by North Korea, United Nations Security Council Resolution (UNSCR) 2321 (2016) requires UN member states to stop scientific collaboration with North Korean individuals and entities, conduct an assessment of proliferation risks, and consult with the UN sanctions committee before launching any technical cooperation. Implementing these restrictions in academia will require greater cooperation and compliance on both government and institutional levels. While there are many best practices identified by multilateral export control regimes, additional recommendations for enhancing ITT controls in this realm include: 1) a national authority identifying institutes in a collaborative relationship with North Korea and dealing with sensitive technologies; 2) conducting rigorous background screening of North Korean scholars before engaging in academic cooperation; 3) academic institutions establishing a technology control plan (TCP) before hosting North Korean scholars; and 4) raising awareness of US reexport controls by both national authorities and academia.
Why Do ITT Controls Matter, and How Are They Implemented?
As a country’s WMD program evolves toward a mature phase, proliferators’ interests shift from procuring one-time-use physical items to acquiring sensitive technologies. This “controlled technology” is defined as information that is essential to the effective use, indigenous production and maintenance of items necessary for WMDs. The possession of sufficient technologies for domestic WMD programs by proliferators would reduce reliance on procurement from foreign sources, and relevant sanctions and export controls would no longer have the intended impact of impeding progress of military advancement by proliferators.
Technology can be transferred via both tangible and intangible means, and ITT poses especially significant challenges for global nonproliferation efforts. First, it is difficult for export regulators to detect illicit ITT in a timely manner due to the non-physical nature of transactions. Additionally, proliferators can easily spread the technology to other proliferators via electronic means. Moreover, technology does not have an expiration date. Once proliferators gain enough experience and master procedural knowledge related to sensitive items, the knowledge will persist. Lastly, many countries have not implemented ITT controls yet, potentially allowing proliferators to exploit such weak links.
One of the arenas that potentially involve the usage of ITT is academia through joint research, training, sharing data, mentorship, acquiring experience in handling dual-use equipment and participation in sensitive research experiments. One notable example is the Iraqi scientist Dr. Rihab Taha, who acquired her PhD in England in the 1970s with a focus on plant pathogens and became the head of the Iraqi biological weapons program in the 1980s. North Korea also actively seeks the acquisition of sensitive technologies through ITT, especially through academic collaborations with foreign institutes and scholars. More specifically, the UN POE noted that North Korean scientists have published several articles through joint studies with foreign scholars in the areas related to nuclear and missile applications and that Kim Il Sung University’s institutional cooperation with universities abroad also poses potential proliferation concerns.
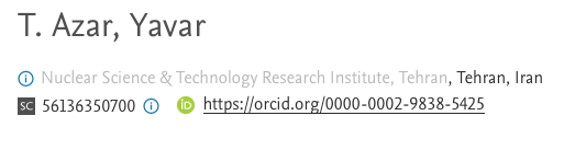
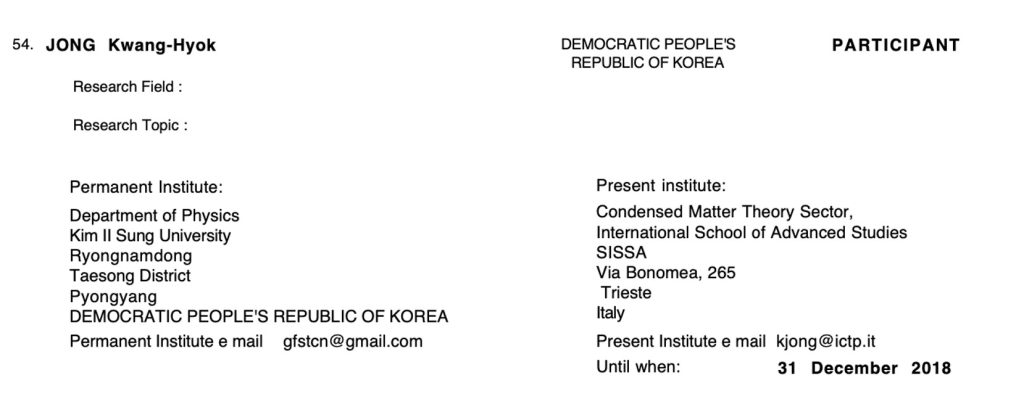
Moreover, open-source information also indicates that North Korean scholars are still associated with foreign research institutes and continued scientific collaborations. For instance, North Korean scholar (or student) Jong Kwang Hyok is or was possibly affiliated with two Italian institutes, the Abdus Salam International Centre for Theoretical Physics (ICTP) and Scuola Internazionale Superiore di Studi Avanzati, and conducted joint research with foreign scholars from various countries until as recently as 2020. There is also information suggesting that one of Jong’s academic partners, T. Azar, Yavar, might be affiliated with the Nuclear Science and Technology Research Institute (NSTRI) in Iran, which is currently under sanctions by the US Department of the Treasury.[1] As a reflection of these realities, the UNSCR 2321 prohibits scientific collaboration with North Korean individuals or groups officially sponsored by or representing the North Korean government, and UN member states should notify the Sanctions Committee of such activities (Appendix 1).
However, despite the importance of ITT controls, not all countries have an adequate legal framework for ensuring that such controls are in place, which can be exploited by North Korea. In addition to the UNSCR 2321, there are several international instruments that provide the legal grounds to implement ITT controls. For example, UNSCR 1718 (2006), which imposes sanctions on North Korea, requires UN member states to control technology transfers to North Korea.[2] UNSCR 1540 (2004) obligates all UN member states to have export controls—including technology controls—in order to prevent non-state actors from acquiring WMD-related items.[3] However, implementing such instruments is subject to the interpretation and discretion of UN member states in terms of establishing jurisdictions over the types of transactions and individuals incurring these controls.
Meanwhile, there are other countries that have been rigorously implementing ITT controls. The United States’ dual-use export control regulation defines “exports” as covering not only cross-border transactions, such as taking physical items out of the country, but also transfers of technology to foreigners within the country, also known as “deemed exports.” Therefore, making sensitive technology available to foreign nationals within the territory of the United States requires a technology holder to obtain an export license from the regulatory authority. Many US companies, universities and research institutes exercise enhanced due diligence by establishing an internal compliance program (ICP) to comply with the deemed export controls. The European Union (EU), South Korea and other countries have also established adequate legal frameworks for ITT controls and are making an effort to prevent proliferation in the academic domain (Appendix 2).
The United Kingdom prohibits ITT involving proliferation activities through immigration controls by establishing the Academic Technology Approval Scheme (ATAS.) The ATAS requires international students admitted to programs involving sensitive subjects to obtain an ATAS certificate from the government of the United Kingdom and to submit the certificate as a part of visa application materials. The immigration law of the United Kingdom prohibits universities from allowing students without a certificate to take courses subject to the ATAS.
Key Considerations of Academic Collaboration With North Korea
In 2006, the Wassenaar Arrangement (WA) introduced a document that puts forward best practices for ITT controls, such as the establishment of a legal framework, post-export compliance monitoring, international cooperation and outreach to industries and academia. Not all countries might be in a position to readily adopt all the measures stated in the WA’s document. However, encouraging those in academia to implement ITT controls and/or self-regulation as the first line of defense might be a less onerous task to implement than other measures. Once a national regulator identifies the research institutes and universities that possess sensitive technologies, the regulator should ensure that these institutes take into account at least three of the factors listed below when considering collaborating with North Korean entities or individuals on the academic level.
Background Screening
Universities and research institutes should conduct an extensive background screening of potential academic partners from North Korea before embarking on academic collaborations. There are several checkbox items, such as identifying if a North Korean scholar has worked on sensitive topics or has connections with other scholars working on sensitive issues. In this regard, academic track records, including a scholar’s publication list and academic collaboration partners, could be suitable reference materials in the risk assessment process.
For example, suppose a foreign university is considering embarking on a scientific collaboration with North Korean scholars for nuclear fusion research (Appendix 3). If the proposed research is going to include anyone involved in lithium-6 research (Appendix 4), the possible cooperation with those individuals could be diverted toward military applications. Meanwhile, the planned research project may pose fewer proliferation concerns if the study only involves researchers working on magnetic confinement fusion (MCF) (Appendix 4) because MCF is a branch of fusion research related to civilian applications. According to UNSCR 2321, once the potential academic exchange plan with North Korea is identified as risk-free, the foreign partner should report to the UN Sanctions Committee its intent to embark on such collaborations.[4]
Technology Control Plan (TCP)
Once a decision is made to collaborate academically with North Korea, a university and research institute should prepare a technology control plan (TCP), which is a document that formalizes procedures and processes to protect restricted technology from being accessed by unauthorized individuals. For example, TCP-related tasks include the physical protection of a laboratory and its hardware, encryption of sensitive data and limiting the scope and topics of conversation with unauthorized people. Having a TCP is particularly important since there is a risk that North Korean scholars who do not represent their government or do not have experience in proliferation activities may still attempt to acquire access to sensitive technology. The latest UN POE report pointed out that the North Korean regime orders its scholars and students abroad to send reports back to the country.
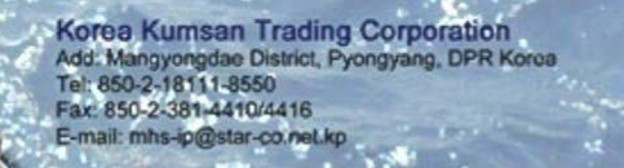
Open-source information also suggests that a particular email address is shared among North Korean scholars and is directly and indirectly related to North Korean entities beyond academia. For instance, the aforementioned North Korean scholar, Jong Kwang Hyok, used [email protected] as his permanent institute email address, which was also found to be used by other DPRK scholars, such as one who participated in an academic event in Italy in 2015. Moreover, this email address is also the contact point for Chongsin Information Technology Agency, whose fax number is identical to that of several sanctioned entities, such as Mansudae Art Studio, Korea Ocean Maritime Management Company and Korea Kumsan Trading Corporation. This implies that no North Korean scholar can be completely free of the regime’s influence, which poses a potential risk of unintended transfers of technology to North Korea without a proper TCP (Appendix 6).
US Reexport Controls
Foreign universities and research institutes should be aware of any equipment or technologies containing US-origin items in their facilities and place appropriate controls over them in order to prevent unauthorized access by North Korean scholars. In general, the US exercises extraterritorial export control jurisdiction over any items originating from the country. US export control regulations define transfers of US-origin items from one foreign country to another foreign country as a “reexport” and require licenses for such transactions. In other words, if a foreign academic institute transfers or releases any items, except for food and medicines, that contain US-origin technology or goods to North Korean nationals without permission from the US government, it may constitute a violation of US reexport controls, regardless of where the items are located.
There are indications that North Korean scientists might be interested in utilizing items of US origin for nuclear-related applications. For instance, the studies published under the Atomic Energy Section in the Journal of Kim Il Sung University contain some words that possibly represent the product codes of microcircuits manufactured by US companies, as shown in Appendix 7. The potential US-origin microprocessors identified in Appendix 7 could be categorized into three groups: 1) items listed on both the US national control list and the UN sanctions lists; 2) items that appear on the US control list but not on the UN sanctions lists; and 3) items that are not listed on either list. Academia should be mindful that all three categories of items necessitate reexport license considerations when giving access or transferring to North Korean scholars because any non-listed US-origin items are subject to the US export regulations (called EAR 99 items).
Conclusion
ITT controls are an important mechanism for impeding North Korea’s advancement in developing indigenous WMD production and maintenance capabilities. Although it is desirable to implement ITT controls, countries with less evolved export control systems may encounter difficulties in readily implementing them. In such cases, national authorities reaching out to universities and research institutes could be a practical step in helping to raise awareness about the importance of ITT controls and nonproliferation efforts concerning North Korea. At the same time, it is especially important for academic institutions to do their due diligence as well in terms of conducting thorough background screenings of North Korean nationals and entities, preparing TCPs to limit access to sensitive information by unauthorized North Koreans, and building their own awareness of US reexport control requirements.
***
DOWNLOAD PDF OF APPENDICES HERE, OR VIEW BELOW
Appendix 1. Examples of regulations that control ITT.
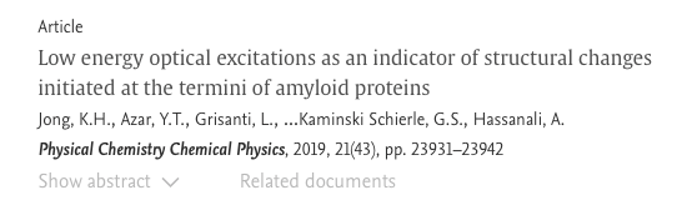
Academic collaboration between Jong Kwang Hyok and foreign scholars.
Azar’s affiliation with an Iranian entity related to nuclear technology.
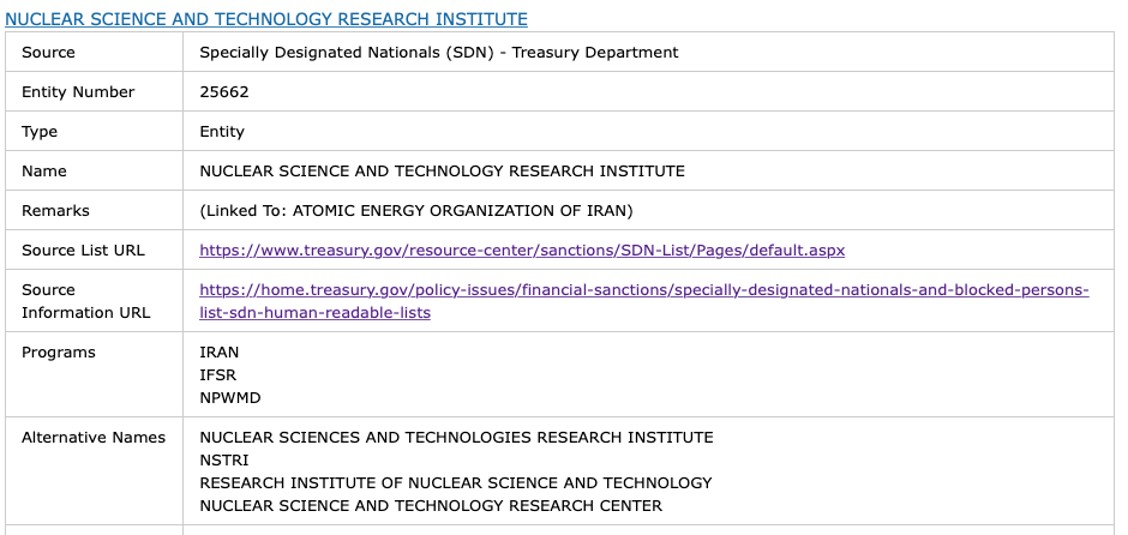
NSTRI sanctioned by the US Department of the Treasury.
Appendix 2. Examples of regulations that control ITT.
Section 734.13 (a) of the United States Export Administration Regulations (EAR)
… Export means:
(1) An actual shipment or transmission out of the United States, including the sending or taking of an item out of the United States, in any manner;
(2) Releasing or otherwise transferring “technology” or source code (but not object code) to a foreign person in the United States (a “deemed export”);…
Article 19 (1) of the Foreign Trade Law of the Republic of Korea
… Any person who intends to export…shall obtain permission…
-
- Transfer from Korea to a foreign country;
- Transfer from a national of the Republic of Korea (including a legal entity established pursuant to domestic laws) to a foreigner (including a legal entity established pursuant to foreign laws) in the Republic of Korea or a foreign country.
Article 32-3 of the Enforcement Decree of the Foreign Trade Act of the Republic of Korea
…transferred by any of the following methods:
-
- Transfer through an information network, such as telephone, fax, and email;
- Transfer through discourse or act, such as direction, education, training, and presentation;
- Transfer through recording devices, such as paper, film, magnetic disc, optical disc, and semiconductor memory apparatus, or through a computer and other information processing devices.
Article 2 (10) of Regulation (EU) 2021/821
… “exporter” means:
(a) any natural or legal person or any partnership that, at the time when the export declaration or the re-export declaration or an exit summary declaration is accepted, holds the contract with the consignee in the third country and has the power to determine the sending of the items out of the customs territory of the Union; where no export contract has been concluded or if the holder of the contract does not act on its own behalf, exporter means the person who has the power to determine the sending of the items out of the customs territory of the Union; or
(b) any natural or legal person or any partnership that decides to transmit software or technology by electronic media, including by fax, telephone, electronic mail or by any other electronic means to a destination outside the customs territory of the Union or to make available in an electronic form such software and technology to natural or legal persons or to partnerships outside the customs territory of the Union.
…”provider of technical assistance” means:
(a) any natural or legal person or any partnership that provides technical assistance from the customs territory of the Union into the territory of a third country;
(b) any natural or legal person or any partnership resident or established in a Member State that provides technical assistance within the territory of a third country; or
(c) any natural or legal person or any partnership resident or established in a Member State that provides technical assistance to a resident of a third country temporarily present in the customs territory of the Union.
Appendix 4. Domestic Network of North Korean Nuclear Scientists.
The chart below shows the network of North Korean nuclear scholars. It has been constructed based on publication records. The size of each node indicates the total number of articles published in collaboration with other scholars. The thickness of each line between nodes represents the number of collaborative publications between two nodes. The node colors range from yellow to red, and the closer a node is to red indicates that the studies conducted by the respective scholar contain more select sensitive keywords, which are listed in Appendix 5. For easier viewing, the network chart below only focuses on studies published between 2013 and 2017. The different node colors do not definitively determine the level of proliferation risks.
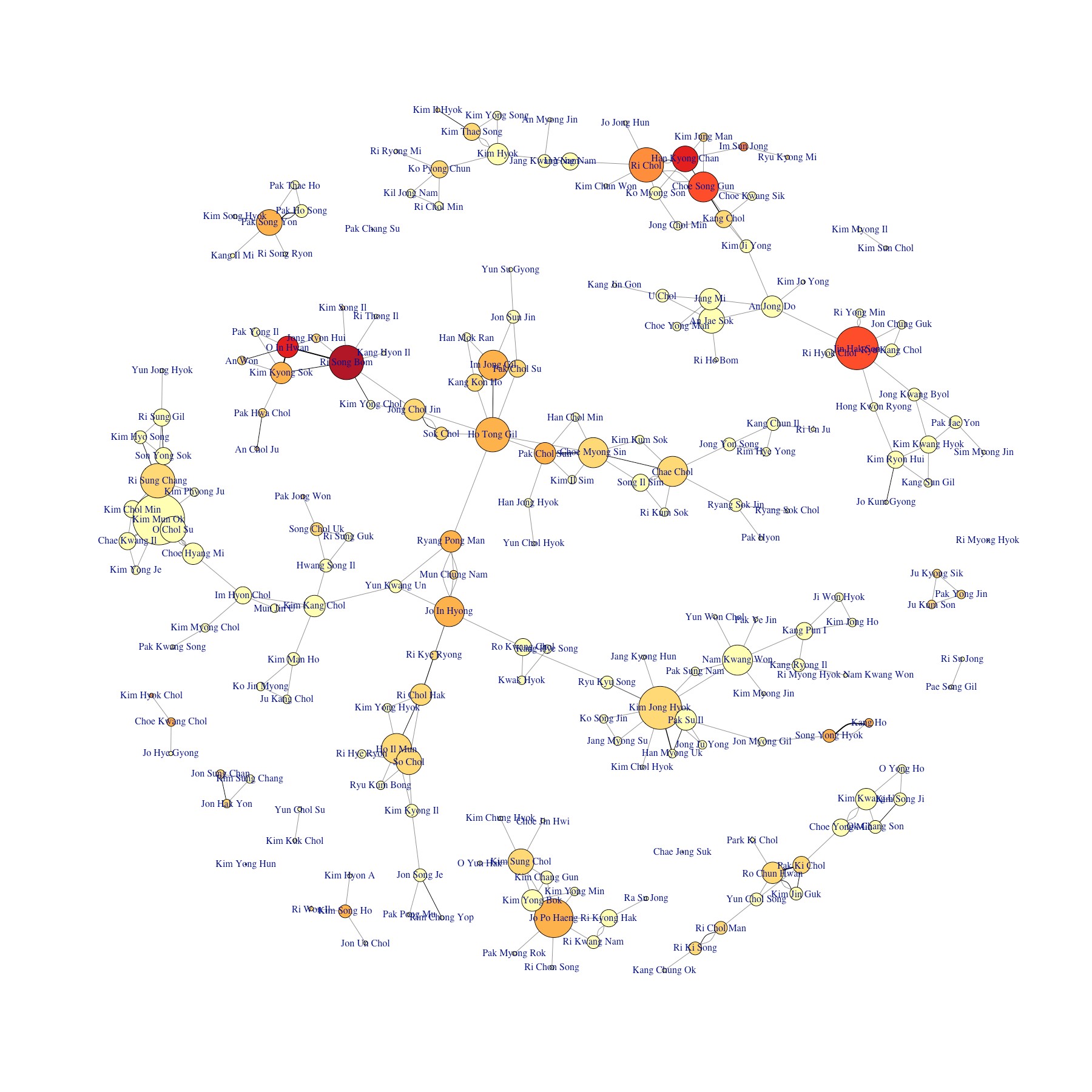
The sub-community represented by Ri Chol, Han Kyong Chan, and Choe Song Gun is related to lithium-6 research, while the sub-community covering Kim Mun Ok and O Chol Su focuses on MCF and other basic fusion-related studies.
Appendix 6. North Korean contact information shared among multiple individuals and entities.
Jong Kwang Hyok’s contact information.
Flyer from the Chongshin Informatics Centre.

Korea Kumsan Trading Corporation information.
Appendix 7: Indications of North Korean scholars using possibly US-origin items in nuclear research.
(Disclaimer: The author of this article cannot guarantee the validity of the information found in Appendix 7. Any similarity to the names of any real products or entities is purely coincidental.)
- [1]
See “T.Azar, Yavar,” Scopus, https://www.scopus.com/authid/detail.uri?authorId=56136350700; “Specially Designated Nationals And Blocked Persons List (SDN) Human Readable Lists,” US Department of the Treasury, https://home.treasury.gov/policy-issues/financial-sanctions/specially-designated-nationals-and-blocked-persons-list-sdn-human-readable-lists; and “Sanctions List Search,” Office of Foreign Assets Control, https://sanctionssearch.ofac.treas.gov/Details.aspx?id=25662.
- [2]
See United Nations, Security Council, Resolution 1718, S/RES/1718, October 14, 2006, https://undocs.org/S/RES/1718(2006); and United Nations, Security Council, Letter dated 13 October 2006 from the Permanent Representative of France to the United Nations addressed to the President of the Security Council, S/2006/814, October 13, 2006, https://undocs.org/S/2006/814.
- [3]
UNSCR 1540 defines “related materials” as: “materials, equipment and technology covered by relevant multilateral treaties and arrangements, or included on national control lists, which could be used for the design, development, production or use of nuclear, chemical and biological weapons and their means of delivery.”
- [4]
More in-depth analysis and the datasets are available here.
